Disclaimer : This post is only for the educational purpose.
All data and information provided on amazingtricks.in blog are for informational purposes only. Amazingtricks will not be responsible for any action performed by any reader.
How to DDOS an IP using HOIC: A distributed denial of service (DDOS) attack involves a group of compromised systems usually infected with Trojans used to perform a DoS attack on a target system or network.
DDOS is a sophisticated and complex attack based on attack and multiple distributed attack sources. In a DDOS attack, a large number of compromised computers (zombies) are involved to interrupt or suspend network services.
In the previous post, we just have given a light view of a DDOS attack. Here we will deeply understand DDOS attacks without harming the infrastructure. We will use the help of a virtual box so that no infrastructure will be harmed.
Step1: Installing Requirements
Installing Virtual Box: Goto this https://www.virtualbox.org/wiki/Downloads and download the Virtual Box depends on your operating system and install it in your System
Installing Kali Linux : Goto this https://www.kali.org/downloads/ and download the image file of your type and install it.
There is another way of install kali in virtual box that is you can directly import the .ova file to virtual box.
Goto this https://www.offensive-security.com/kali-linux-vm-vmware-virtualbox-image-download/#1572305786534-030ce714-cc3b and Download the Virtual Box image file and import it.
Installing Windows 10: If you are having a windows operating system then no need to install it in a virtual box. If not install the windows 10 in virtual Box.
Installing HOIC in Windows: Goto this https://github.com/170030262/hackthebox/blob/master/HighOrbitIonCannon(HOIC).zip and download the HOIC in windows os.
Step2: Configuring for the Attack.
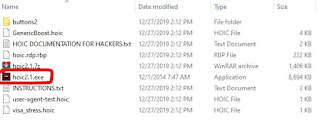
In the Windows Operating System Extract the Zip file and open the HOIC folder .
double click on the “hoic2.1.exe” and run the HOIC application.
Once the HOIC GUI appears on the screen, click “+” below TARGETS
The HOIC Target pop-up appears. Type the target URL” https://[IP Address of the target machine]” in the URL field, slide the power bar to High, select “GenericBoost.hoic” booster from the drop-down list, and click Add.
Note: The IP address entered in this lab is that of the Kali-Linux virtual machine .
To get the ip address of kali machine open kali terminal and type “ifconfig” and enter .
Set the THREAD value to 20
click the “FIRE TEH LAZER!” toinitialize the attack. .
This initiates the DDoS attack on the target Kali Linux machine.
Step3: Observing the Attack
Switch to the Kali Linux virtual machine, and launch the command-line terminal.
Type Wireshark in the terminal, and press Enter. If an Error pop-up appears, click OK.
The Wireshark GUI appears; select a network interface and click Start.
Observe that Wireshark starts capturing a large volume of packets, which means the machine is experiencing a huge number of incoming packets. These packets are coming from the Windows virtual machine.
Leave the machine intact for 5–10 minutes, and then open it again.
When you have completed click FIRE TEH LAZER! again, and then close the HOIC window in the windows machine. Also, close the Wireshark window in Kali Linux.
Step4: Conclusion
In real-time, a group of hackers operating hundreds or thousands of machines configure this tool on their machines, communicate with each other through IRCs, and simulate the DDoS attack by flooding a target machine/website at the same time. The larger the number of attacker machines, the higher the impact of the attack on the target machine/website.